I received a call today from the Fraud Prevention service of my credit card company, saying that “someone” called in to Customer Service, posing as me, and attempted to gather information about my account. This person had my credit card number, but failed to get past the additional security questions asked by the support staff. The support staff then promptly called me, and asked if it was I who tried to call in to Customer Service. The moment I said “no,” the operator told me that my account will be immediately deactivated to prevent any fraudulent charges, and that a new credit card would be mailed to me within 5 business days.
Despite the inconvenience of having my credit card account shut down, and being issued a new card, I applaud the support staff for taking their users’ security so seriously. But this incident also got me thinking about the current level of security used by online retailers, as well as online banking and credit card websites. After all, how exactly did a would-be identity thief get a hold of my credit card number? All of my online purchases are through very reputable stores like Amazon and Newegg. All the items I purchase are completely legal — i.e. no kinky horse-on-girl porn from shady Russian websites. All of my transactions are over SSL, and I’m quite sure that I don’t have a keylogger installed on my system.
This leads to one of the following conclusions, arranged from least to most likely:
- Someone cracked my SSL session with an online retailer. This is astronomically unlikely, but still possible.
- Someone hacked one of the online retailer’s servers, and retrieved the raw database of credit card numbers for thousands of customers.
- Someone hacked one of the company’s servers, and retrieved password hashes for thousands of users, and decoded the passwords at his/her own leisure. If the hacker is an employee of the company, no hacking would even be necessary. The database would be readily available for copying and selling to the black market.
As the incredibly eye-opening Ophcrack project has shown, old-style passwords are no longer safe (i.e. passwords shorter than 15 characters, consisting only of letters and numbers). Any Windows system administrator who hasn’t disabled LM Hashes has been living in a cave, and any Linux administrator who isn’t using shadow passwords is almost equally neglectful. And of course, any administrator or developer who stores users’ passwords in plain-text format should be fired on the spot, and have the infraction recorded as a felony in his criminal record.
The point is, many forms of identity theft can be prevented by using strong passwords — that is, passwords that are generously long (15 or more characters), that contain uppercase and lowercase letters, numbers, and special characters like $, %, &, space, and maybe even exténdeð characters, or even Unicode!
The question is, are online retailers and banking websites “ready” for strong passwords?
No!
At least that’s the short answer. As an example, let’s take a look at what happened when I tried to change my password on my banking website, which happens to be Huntington. I typed in a strong password with letters, numbers, and special characters, and this is what I got:
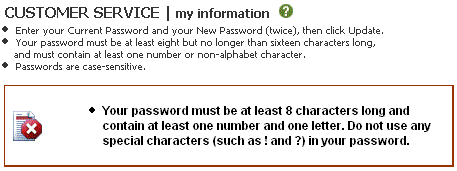 I beg your pardon?! Of all the websites in the world, banking sites should be the most secure by definition. And yet, here we are with Huntington’s website telling us to limit our password to 16 characters, and not use any special characters!
I beg your pardon?! Of all the websites in the world, banking sites should be the most secure by definition. And yet, here we are with Huntington’s website telling us to limit our password to 16 characters, and not use any special characters!
In Huntington’s defense, they do provide an additional level of security by asking a secret question (in addition to the password), if a user logs in from a different IP.
I can understand enforcing minimum requirements for password strength, which Huntington does, but setting limitations on password strength? What gives?
Let’s move on to my credit card website, which is Chase. Attempting to change my password there, I get the following:
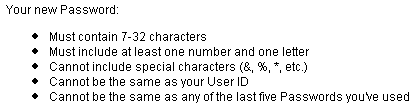 Again, they tell us not to use special characters, and to limit the length of our password. Even though the length limitation here is 32 characters, my question is why is there a length limitation? And why can’t special characters be used?
Again, they tell us not to use special characters, and to limit the length of our password. Even though the length limitation here is 32 characters, my question is why is there a length limitation? And why can’t special characters be used?
If the excuse is that the underlying software that runs the website doesn’t support passwords with special characters, then the software is in serious need of revision. The password hashing algorithm should not care about what characters are passed into it.
I’m a big fan of passphrases, too — that is, passwords like “How many licks does it take?” or “Density = Mass/Volume” or “E = m*c^2”, all of which are much stronger than passwords of equal length with just letters and numbers. But, since these websites don’t allow passphrases, I’m forced to come up with a weaker password that fits all their guidelines and restrictions. Even worse, since each website may have slightly different restrictions on passwords, I’m forced to come up with a least-common-denominator password if I want to use one password for multiple sites.
With this kind of “password mess” on the most secure internet websites, it’s no wonder ordinary users become confused about what kind of passwords they are and aren’t allowed to use, and default to using common, easy-to-remember passwords that are just waiting to be cracked by malicious individuals.
 To change this graphic, use P2K Commander to navigate to the phone’s file system (“/a”) and go to the “mobile” directory.
To change this graphic, use P2K Commander to navigate to the phone’s file system (“/a”) and go to the “mobile” directory. Short of reprogramming the phone’s firmware, there’s no end to the customizations you can make to your V3xx by simply editing or replacing certain files in the phone’s filesystem using P2K Commander. As always, don’t forget to back up any files you edit or replace. Enjoy!
Short of reprogramming the phone’s firmware, there’s no end to the customizations you can make to your V3xx by simply editing or replacing certain files in the phone’s filesystem using P2K Commander. As always, don’t forget to back up any files you edit or replace. Enjoy!